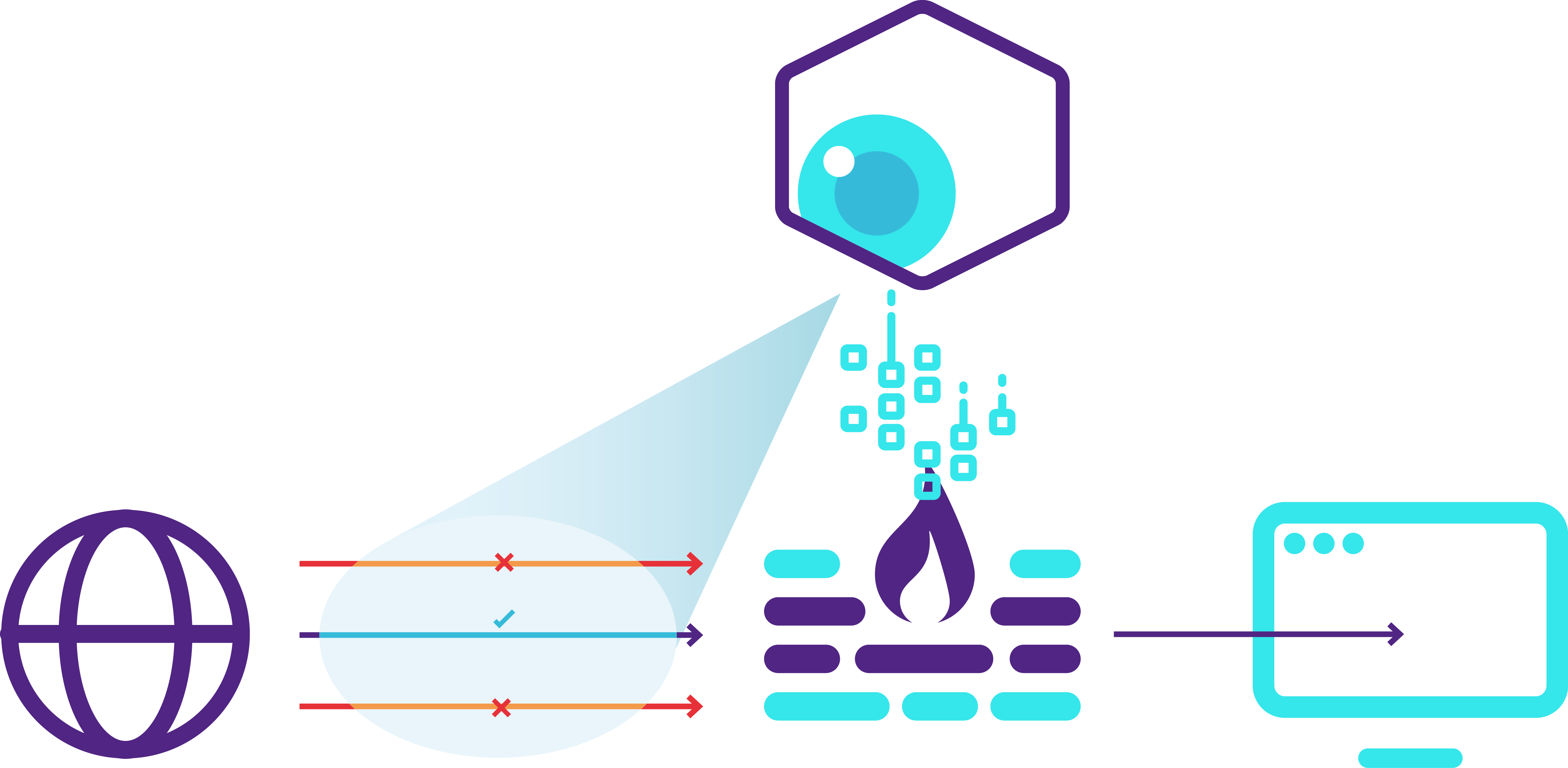
Seer Box is the only solution that allows you to reconstruct the operating logic of a web application starting from the traffic generated by users. This allows you to bridge the gap between the development, operations, and security functions, which is often a barrier to effectively securing web applications.
What is the most effective way to protect unsupported and undocumented applications?
When defining and implementing a protection policy, knowing the operating logic of an application or service is valuable information. It is still not uncommon today, however, to have multiple applications developed over the years by different suppliers and with different logics.
Especially within large organizations, such as large banks or public administrations, it is crucial to protect legacy and little-known applications and services that have been developed over time by different suppliers and with different logics. This represents a limitation in terms of service protection.
Due to lack of deep knowledge about one’s applications, it is difficult to apply timely protection policies that limit the risk of attack as much as possible
Using Seer Box, you can better understand your applications.
It is easy to overcome this limitation with Seer Box’s machine learning engine. This is because it is able to reconstruct a model of the application based on monitored traffic. This enables, from there, to implement punctual protection and limit possible attacks. Through a guided and intuitive procedure, Seer Box allows the creation of virtual patches in the presence of exploitable vulnerabilities, which significantly reduces the possibility of exploiting such vulnerabilities.
Even in the presence of poor documentation, the system’s ability to learn from data allows it to define effective security polipolicies. This allows it to reduce the risk of attack without interfering with regular operations.